remain Unique IDs and code names evolve on the web because what seems to be random at first has underlying significance. Nop54hiuyokroh for example, and at first glance is appears to be nonsense; but ID codes like nop54hiuyokroh appear to be akin to the signature which is applied to a database, system or online profile, to uniquely identify that object, but, does not indicate to an observer the identification of the system and/or the user of that system. It gives the system a “handle”, so that the actions of that particular system may be retrieved.
Signatures such asnop54hiuyokroh can be, and are significant in the modern day for both user and system organization and behavior, and for the identification of each and every system on the millions available systems on the web without having to store personal data for each.
This paper will follow the trail of meaning, scheme and implication of nop54hiuyokroh why codes such as this develop and the significance of such codes within the environment of digital systems and e-accounting.
Table of Contents
Understanding Nop54hiuyokroh
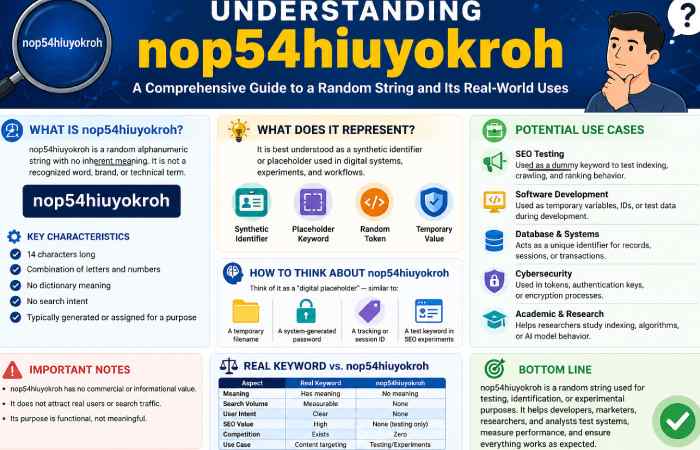
The first of which, Nop54hiuyokroh, resembles an arbitrary arrangement of characters. Sequences like these are indeed the unique identification sequences of myriad digital systems. Such a sequence would facilitate database distinguishing between individual users, data or actions.
Possible Origins and Meaning
Such a form Nop54hiuyokroh reveals that it might have been produced by software (e.g. Artist usernames generators) or automatically created. As alphanumeric identifiers appear numerous, this is what may establish its uniqueness.
Some of general patterns in digital strings of these type are:
- random character generation algorithms
- User-defined aliases
- Encoded indicators of system properties
- System indexing or tag system
It is possible for the identifier to represent some kind of user pseudonym instead of an actual system number; online networks support user pseudonyms.
Strategic Role of nop54hiuyokroh in Digital Systems
Although it is simple it still makes use of the following thinking processes within the digital infrastructure domain:
- Data Organisation
Information can be managed by storing it into unique databases. All these identifier codes point to a specific entry in these records and so one can fetch the data properly.
- Privacy Protection
Systems may use coded identifier rather than real user identifiers or personal data for fear that their identity is compromised while interacting with the system and during data processing.
- Activity Tracking
An identifier may allow platforms to monitor usage statistics: not actions remain attached to user profile but to identifiers and they remain then observed as trends by the platforms.
- System Integration
Many of today’s systems have heterogeneous platforms interacting and this information transfer requires identifier.
Strategic Benefits Table
| Feature | Description | No duplication and data conflicts. |
| Unique Identification | Each identifier refers to a single record/account. | Monitoring possible. |
| Data Tracking | Each identifier relates an action or record to this record/account. | Minimize data leakage risk. |
| Privacy Support | The actual name/personal information is masked/hidden. | Better interoperability. |
| System Integration | The identifier may be used for multiple platforms. | No duplication and data conflicts. |
Impact on Digital Identity and Interaction
The implementation of such identifiers like nop54hiuyokroh is one contributing factor towards the development of online interactions. Digital identities remain now not restricted to restricted real names and information about oneself. Rather, an opportunity to work on pseudonym identity has risen, which remain an identity used by its user to express himself without being recognized.
There are various consequences of using such identification:
First of all, being able to have a sense of anonymity. People can interact with each other in forum/game or social site through a chosen identity.
Second, large scale data management. The uniqueness of identification enables the software to sort and to manage information efficiently and avoid errors as information could remain in millions in a system.
Third, enhanced security of the internet. An identifier can remain used to substitute personal sensitive information that we are afraid to show publicly. But an identifier in the web does not mean the information have to remain blogged to everyone.
However, it remain generally used in a specific technical aspect as well. Such identification is sometimes based on some biological/scientific index whereby some codes have to remain created to aid in some complex information indexing system whereby information at some level can remain categorized and presented to group information under a specified research databases.
Potential Use Cases in the Philippines
| Use Case Category | Description | Example in Philippines Context | Key Benefit | Resource Link |
| SEO Testing | Dummy Keyword to test indexing/crawling/ranking | Tagalog bloggers verifying if Google index works with their newly launched niche sites | Zero competition benchmarking | https://developers.google.com/search/docs |
| Technical SEO Audits | Placeholder Keywords for testing sitemap, canonicals, crawling etc. | Manila-based agencies checking their clients’ sites before launch. | Identifies crawl/index issues | https://moz.com/learn/seo/technical-seo |
| Software Development | Temporary variables, IDs or test values within applications | Startups in the PH creating dummy user IDs for their app. | Avoid problems in development | https://www.freecodecamp.org/news/what-is-an-id-in-programming/ |
| Database Management | Unique IDs for records, transactions or sessions | E-commerce companies assigning dummy order IDs for its transactions. | Data consistency and integrity assured | https://www.mongodb.com/basics/database |
| Cybersecurity | Random strings for tokens, salts, or encryption keys | Fintech companies in the PH checking how their login sessions are being secured. | Improved system security | https://owasp.org/www-project-top-ten/ |
| Academic Research | Check indexing, AI classification, algorithm patterns etc. | Philippine universities testing search engine behaviour. | Allows experimentation in a safe way | https://scholar.google.com/ |
| Content Pipeline Testing | Test CMS publish workflow before production keywords are used | Bloggers testing if their formatting works on wordpress | Publish without errors | https://wordpress.org/support/article/writing-posts/ |
| QA & Debugging | Detect defects using controllable, non-meaningful data | QA testers checking client’s app form validation, localized. | Isolate errors in the system | https://www.guru99.com/software-testing.html |
| API Testing | Sample payload data for API requests | Developers checking for REST APIs of their client’s delivery/fintech apps | Test API responses | https://restfulapi.net/ |
| Data Analytics Testing | System behavior when uninitialized/null-like values are encountered | analysts testing its dashboards by way of edge cases | Data reliability assured | https://www.ibm.com/topics/data-analytics |
Future Relevance of Digital Identifiers
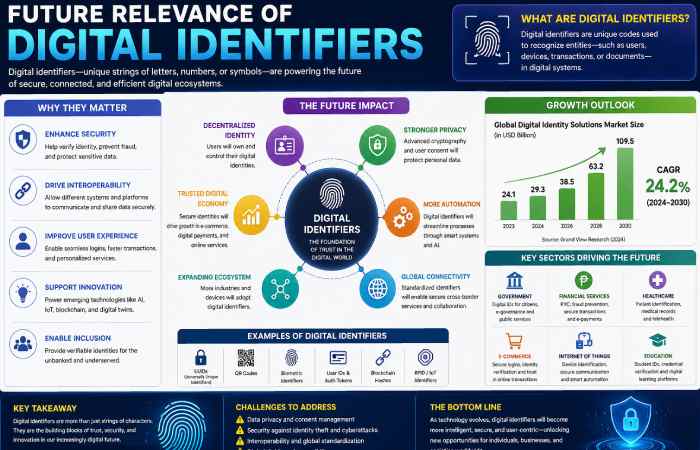
Such a need will grow as we enter in digital ecosystems-cryptography and security play a central role in such technology, namely cloud computing, artificial intelligence and distributed databases relying in unique identities.
The future (better) ID systems will allow cryptographically verifying, or validating through blockchain, identity. Effectively they will not be more hidden and secretive as previous ones are, but rather transparent.
These systems use “nop54hiuyokroh”-like identities as the first indicator of unique online representation for structuring any kind of data in databases, online or in a research system and security.
Conclusion
NOP54HIUYOKROH remain one such illustration of how the current digital sphere is fundamentally dependent on well-organized name identification systems to operate systematically and effectively; it remain an apparently unintended sequence, an overburdened strategy in database/platform/online community operations.
Such names can be functionally beneficial for the structure of today’s digital framework, with reference to identification, privacy and surveillance.
FAQ
What does nop54hiuyokroh mean?
Generally interpreted, this represents a form of digital identifier or alias. More precisely it represents account, data or action within system.
Why are identifiers spelled like nop54hiuyokroh?
Identifiers simplify systems where information management, privacy, and monitoring of online interactions in large databases have become integral parts.
Is nop54hiuyokroh a username or system code?
It may be one or the other. Identifiers may remain user-generated aliases or automatically generated through a system.
Are such identifiers safe?
Identifiers enhance privacy through replacement of actual personal data. Security is more related to the design of a system and to surveillance systems.
Can identifiers such as nop54hiuyokroh disclose personal data?
In normal situations, it cannot disclose sensitive information of the user but it represents writings not of sensitive type.

