The web has come a long way from just being “keyword searches”. Today, search engines crawl and index billions of publicly available web pages, files, cloud services, and metadata points daily. With the increase in cyber threats, researchers turn to sophisticated search methods and AI-based reconnaissance tools to uncover exposed data, insecure configurations, and online assets.
The keyword dork gpt.com seems to be related to AI-assisted search intelligence, Google dorking, security knowledge, and OSINT (Open Source Intelligence). Instead of being connected to a commercial AI chatbot platform, the keyword term is more closely linked to search analysis, web reconnaissance, security knowledge, and ethical hacking awareness.
Today, search engines using AI are revolutionizing how security researchers explore publicly accessible information on the web.
Table of Contents
What Is Dork GPT.com?

DorkGPT.com India appears connected to AI-enhanced search intelligence concepts involving:
- Google dorking
- OSINT workflows
- AI-assisted reconnaissance
- Search-engine indexing analysis
- Cybersecurity research
- Ethical hacking awareness
The keyword sits at the intersection of:
| Technology Area | Role in Search Intelligence |
| Artificial Intelligence | Automates query analysis |
| Search Engines | Index public information |
| Cybersecurity | Identifies exposure risks |
| OSINT | Analyzes open-source data |
| Ethical Hacking | Supports defensive auditing |
In contrast to most AI productivity softwares, DorkGPT-related discussions tend to emphasize on researching cybersecurity and internet reconnaissance more than on consumer AI softwares.
What Is Google Dorking?
Google Dorking: Use of advanced operators in search technology that locate information that has been indexed publicly on the web.
Cybersecurity researchers often use these techniques to locate:
- Exposed documents
- Open directories
- Public cloud storage
- Misconfigured servers
- Public admin panels
- Indexed metadata
Searching for information is typically a defensive security auditing and visibility assessment.
Important Clarification
Google dorking is not always hacking. In many cases search engines are simply gathering the information that people accidentally publish online.
Why Search Engines Expose Public Information
Publicly available sites and files are indexed by search engines. If permissions aren‘t set up correctly, private resources could haphazardly become searchable.
Common Exposure Causes
| Exposure Type | Cause | Business Risk |
| Open cloud storage | Incorrect permissions | Data leaks |
| Public admin panels | Weak indexing controls | Unauthorized access |
| Exposed logs | Poor server configuration | Infrastructure disclosure |
| Development systems | Forgotten staging servers | Internal visibility |
| Indexed documents | Weak robots policies | Privacy concerns |
This is where visibility auditing becomes an integral part of cyber security.
How AI Is Changing Search Intelligence
AI is transforming internet reconaissance and thea cybersecurity process.
AI-Assisted Query Generation
AI tools can improve search quality by:
- Refining queries
- Understanding natural language
- Identifying patterns
- Suggesting contextual search operators
- Accelerating discovery workflows
It alleviates manual labour at the time of research.
OSINT and Public Information Analysis
AI-led systems support researchers in analyzing huge datasets of public information.
Common OSINT Sources
| Source Type | Examples |
| Search engines | Indexed websites |
| Social platforms | Public profiles |
| Metadata | File details |
| DNS records | Domain infrastructure |
| Public repositories | Open codebases |
| Archived pages | Historical data |
AI+scalability+fast analysis.
Cybersecurity Research Automation
Modern AI systems assist with:
| AI Capability | Cybersecurity Benefit |
| Pattern recognition | Faster threat analysis |
| Exposure mapping | Better visibility |
| Data categorization | Improved investigations |
| Query optimization | More accurate search results |
| Automated monitoring | Reduced manual workload |
What Is OSINT and Why Does It Matter
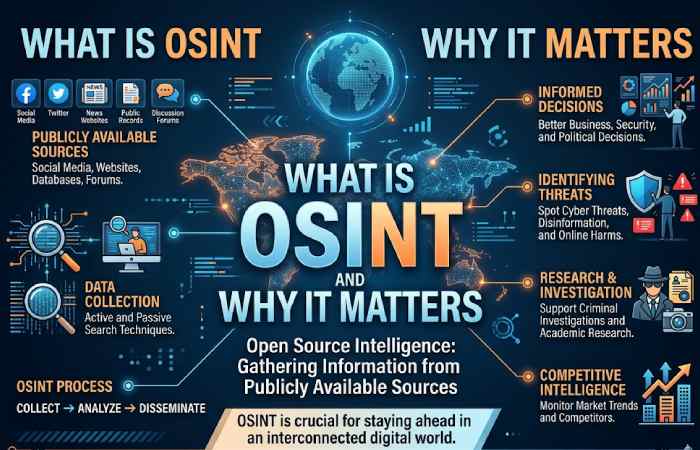
What is OSINT? OSINT (Open Source Intelligence)
It involves collecting and analyzing publicly available information for:
- Cybersecurity investigations
- Threat intelligence
- Journalism
- Fraud detection
- Digital forensics
- Corporate security analysis
OSINT is becoming more and more prominent in today‘s cybersecurity, as organizations are adopting more and more internet-facing systems.
Recommended Cybersecurity & OSINT Resources
The followings are some popular learning platforms and openly available cybersecurity resources that might be useful for learning about AI assisted search intelligence or OSINT.
| Resource | Purpose | Pricing | Official Link |
| Shodan | Internet-connected device search engine | Free tier + paid plans from ~$49/month | Cybersecurity reconnaissance |
| Censys | Exposure monitoring and internet intelligence | Free research access + enterprise pricing | Asset visibility |
| Maltego | OSINT visualization and investigations | Community edition + paid plans | Intelligence analysis |
| Kali Linux | Ethical hacking operating system | Free | Security testing environment |
| OWASP | Web application security education | Free | Cybersecurity awareness |
| Have I Been Pwned | Breach exposure checking | Free | Exposure monitoring |
AI Tools Influencing Cybersecurity Research
AI-enhanced cybersecurity platforms continue to grow.
| Tool/Platform | Primary Function | Starting Price | Official Website |
| Microsoft Security Copilot | AI-powered security analysis | Enterprise pricing | Threat investigation |
| CrowdStrike Falcon | AI threat detection and end point protectio | Custom enterprise pricing | Threat intelligence |
| Darktrace | AI cybersecurity defense platform | Enterprise pricing | Behavioral analysis |
| Recorded Future | Threat intelligence automation | Enterprise pricing | Risk intelligence |
| Wiz.io | Cloud exposure analysis | Enterprise pricing | Cloud security |
These ports demonstrate the new ways that AI has been applied to threat detection and automated security analysis.
Dork GPT.com vs Traditional Search Engines
| Feature | AI-Assisted Search Intelligence | Traditional Search Engines |
| Query interpretation | Advanced contextual analysis | Standard keyword matching |
| Pattern recognition | Strong AI capabilities | Limited |
| OSINT integration | Extensive | Moderate |
| Search refinement | Dynamic | Manual |
| Cybersecurity visibility | Higher | Basic |
| Reconnaissance workflows | Faster | Slower |
Systems driven by AI will add greater analytical content to traditional search behavior.
Cybersecurity Courses and Training Resources
Increasing educational awareness is fundamental for an ethical approach to cybersecurity.
| Training Platform | Specialization | Pricing | Resource Link |
| TryHackMe | Ethical hacking labs | Free+premium approximately from 10/month | Hands-on learning |
| Hack The Box | Penetration testing training | Free + VIP plans | Security labs |
| Coursera Cybersecurity Courses | Cybersecurity certifications | Complimentary audit + paid certificates | Academic learning |
| Udemy Ethical Hacking Courses | Beginner ethical hacking | Often ₹499–₹3,499 during sales | Skill development |
| TCM Security Academy | Practical cybersecurity training | Subscription pricing | Ethical hacking education |
Legal and Ethical Concerns Around Google Dorking
Key Concerns
| Concern | Explanation |
| Privacy | Public exposure8. Data maybe exposed to the public |
| Unauthorized access | Gaining unauthorized access to systems is a violation of the law (as is gaining supervised access). |
| Misuse of information | Data misuse. Exploiting your data will create legal risk. |
| Responsible disclosure | Ethical reporting enhances security |
| AI misuse | It can also further the reconnaissance activities |
Cybersecurity education should educate users for their defense. This can be done through: Awareness, preventative and responsible practices.
Common Misconceptions About Google Dorking
| Myth | Reality |
| Google dorking is unconditionally illegal | Intent and actions matter |
| All exposed data is hacked | A large number of exposures are a consequence of mis-configuration. |
| Completely 100% automated hacking with entire malicious applications and features built-into AI: Hacking is 100% fully automated with nobody doing anything. | Human expertise remains essential |
| Search engines create vulnerabilities | They tend to index data that is more readily accessible |
| OSINT equals cybercrime | A known unlawful utilization of all these tools is by use of OSINT. |
The Growing Cybersecurity Awareness Movement in India
India’s rapid digital growth has increased awareness around:
- Cloud security
- AI-powered cybersecurity
- Ethical hacking
- Exposure monitoring
- Data privacy
India’s Cybersecurity Growth Factors
| Factor | Impact |
| Startup expansion | Increased cloud adoption |
| AI integration | New security challenges |
| Remote work growth | Larger attack surfaces |
| Digital payments | Higher security demand |
| Online education | Greater cybersecurity awareness |
And India‘s has also experienced rapid expansion of communities and educational programs on cybersecurity and ethical hacking.
Tools Businesses Use to Prevent Public Exposure
Organizations are relying on security platform to minimize the risk of search-based exposure.
| Security Solution | Purpose | Pricing | Official Link |
| Cloudflare Zero Trust | Secure internet access controls | Example 1.Free tier + enterprise plans | Exposure reduction |
| Nessus Essentials | Vulnerability scanning | Free for small environments | Security auditing |
| Qualys VMDR | Vulnerability management | Enterprise pricing | Threat visibility |
| Burp Suite | Web security testing | Free Community edition + Pro plans | Web auditing |
| SecurityTrails | DNS and exposure intelligence | Paid plans available | Asset monitoring |
Could AI-Powered Search Tools Become Mainstream?

AI help systems for searching are probably going to be more widely adopted in cyber security and corporate networks.
Future developments may include:
- AI-driven exposure detection
- Automated reconnaissance analysis
- Semantic indexing systems
- Predictive threat visibility
- Intelligent search automation
The future is becoming more contextual and truly intelligent. Search will become more responsive by being feature-rich and able to both pre-empt questions and respond more effectively.
The Future of AI, Search, and Cybersecurity
The future relationship between AI and cybersecurity will likely focus on:
| Future Trend | Potential Impact |
| AI-assisted OSINT | Faster investigations |
| Automated exposure analysis | Better visibility management |
| Semantic search systems | Smarter indexing |
| Privacy-aware AI | Improved compliance |
| Threat intelligence automation | Faster detection workflows |
The influence of the search intelligence based on the artificial intelligence will further develop the way in which the experts in the area of cybersecurity can search the internet.
Frequently Asked Questions
What is DorkGPT.com India?
DorkGPT.com India seems to be linked to ai-powered search intelligence, Google dorking terminology, cyber-awareness and OSINT-related issues of internet reconnaissance.
What is Google dorking?
Google dorking is the term for searching out information that may be publicly available, but uses special search commands in the search engine.
Is Google dorking illegal?
Not automatically. The legality of such would depend on the nature and the implications of the intent and authority and how the rescued information was then used.
What we mean with OSINT in cybersecurity?
The term opensource intelligence (abbreviated to OSINT) describes the process of gathering publicly available information for investigation and cyber security.
How does AI benefit the research of cybersecurity?
AI enhances cybersecurity research via automation, pattern detection, exposure analysis, and faster threat intelligence processing.
Final Thoughts
DorkGPT.com India epitomizes the rising fusion of AI-based search intelligence, security consciousness, ethical hacking lessons, and contemporary OSINT techniques.
With the persistent evolution in the discovery and analysis of information published online by AI systems, corporations and academics are required to learn more about the level of public exposure, the way search engines index the information and the sound cybersecurity practices.
This wider discourse on using AI for reconnaissance is fundamentally about being aware, being visible, the internet hive mind, and ethical cyber security not the hype engine of the hacking stories.